Industrial security services combine security guards, digital monitoring, and strict entry controls to safeguard your staff, equipment, and facilities. For manufacturing and logistics operations, these services help prevent threats like theft, sabotage, and regulatory violations. This integrated approach ensures your business stays compliant and runs without interruption, even in complex industrial environments.
Industrial Risks in India
- Inventory Shrinkage: High-value raw materials and finished goods often vanish due to internal collusion or porous perimeter control.
- Sabotage: Intentional disruption of machinery or power supplies, often stemming from labor disputes or external actors targeting competitors.
- Compliance Lapses: Failure to maintain documented entry/exit logs or unauthorized access to hazardous areas can trigger severe regulatory penalties under Indian safety norms.
Perimeter Security
The first line of defense is the physical boundary. For industrial facilities, the perimeter is rarely just a fence, it is the first barrier against unauthorized ingress. In Rajesh’s plant, a walk-through revealed rusted chain-link sections and a guard cabin that lacked clear visibility of the loading docks – a classic vulnerability in factory security India.
Effective perimeter security requires a multi-layered approach:
- Hardened Access Control: Integrating RFID-based vehicular access with biometric turnstiles ensures that only authorized personnel enter the production floor.
- Guard Protocols:Guards must be trained in “active vigilance” rather than passive observation. This involves randomized patrolling schedules and mandatory shift-handover documentation.
- Physical Deterrence: High-grade fencing, optimized lighting, and “no-go” zone marking are non-negotiable.
When the perimeter is weak, the breach is rarely forced, it is often opportunistic. By fortifying the entry and exit points with automated booms and under-vehicle surveillance systems (UVSS), managers like Rajesh close the gap where 70% of material leakages occur.
Surveillance Systems
Weeks after upgrading the perimeter, Rajesh installed an AI-enabled video management system. The change in the operational climate was palpable. Surveillance is no longer about recording footage, it is about predictive intelligence.
Modern warehouse security solutions combine physical security with CCTV monitoring and AI analytics to detect anomalies in real time, such as loitering in restricted zones or unauthorized vehicle movement near shipping docks. Data confirms that integrated systems can reduce incidents by up to 25% when supported by a centralized command center.
Before the upgrade, the security team relied on manual reviews of hours of footage after an incident occurred. Post-upgrade, an integrated security setup, combining AI-enabled surveillance with on-ground personnel – enabled real-time breach detection and immediate response, allowing intervention the moment a perimeter violation occurred.
This transition from “forensic” (looking at the past) to “proactive” (preventing the future) is the hallmark of sophisticated plant security services.
Compliance & Safety
Smart Digital Operations systems, as part of a broader digital operations framework, provide the necessary audit trail for compliance readiness:
- Digitized Access & Logs: RFID/biometric-enabled visitor management systems ensure every entry, exit, and movement is securely recorded, creating a tamper-proof audit trail.
- Incident Documentation: Every breach, near-miss, or deviation is digitally logged, categorized, and analyzed, supporting both operational response and compliance audits.
- Integrated Safety & Compliance Monitoring:Systems track PPE compliance, restricted zone access, and critical parameters (such as temperature or equipment conditions), ensuring alignment with industrial safety standards and audit requirements.
Benefits of Industrial Security Services
The objective of professional security is not merely to “watch the gate.” It is to ensure that the facility operates at peak capacity without interruption. When Rajesh implemented a unified security strategy, the quantifiable benefits were immediate:
- Loss Prevention: Inventory shrinkage dropped by 8% within the first two quarters.
- Operational Uptime: By securing the logistics chain, loading and unloading times became predictable, reducing idle time for trucks.
- Workforce Safety: A secure environment reduces workplace accidents, boosting employee morale and retention.
- Compliance Assurance: Annual safety audits became a stress-free administrative process rather than a fire drill.
The “incident” that started Rajesh’s journey – the recurring variance, was resolved not just by catching a thief, but by building a culture of security that deterred the intent to steal in the first place.
How Terrier Handles Industrial Security
Terrier Security Services approaches industrial security not as a static service, but as an operational partner. We understand that a cement plant in a remote location has fundamentally different requirements than a pharmaceutical warehouse in an urban hub.
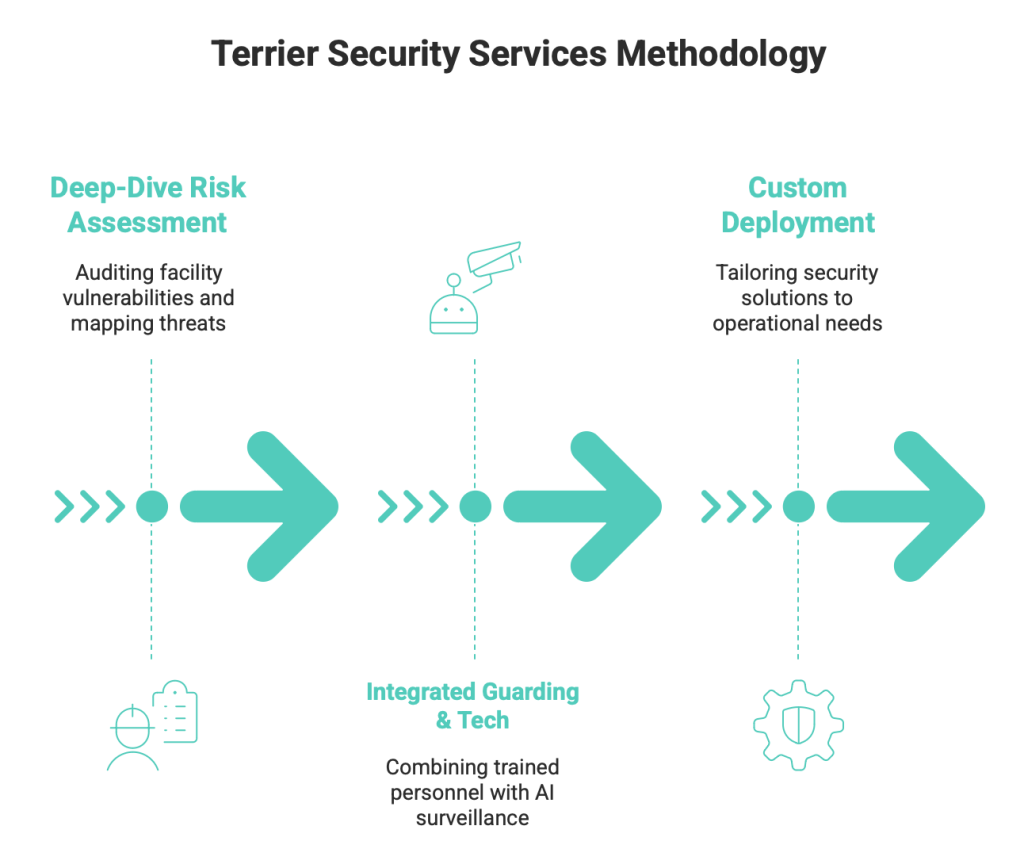
Our methodology includes:
- Deep-Dive Risk Assessment: We begin by auditing your facility’s existing vulnerabilities, mapping them against site-specific threat vectors.
- Integrated Guarding & Tech: We do not believe in replacing humans with tech, or vice versa. We integrate highly trained guarding personnel with modern AI-driven surveillance to create a force multiplier.
- Custom Deployment: Whether you need 24/7 static guarding, perimeter patrol, or supply chain security, we deploy a tailored solution that fits your operational rhythm, not the other way around.
We ensure that your security infrastructure is as resilient as your production line.
Frequently Asked Questions
What is industrial security?
Industrial security refers to the strategic integration of physical and technical measures designed to protect a manufacturing or logistics facility from internal and external threats, including theft, unauthorized access, and sabotage.
How to secure a factory?
Securing a factory requires a layered defense: implement biometric access control for entry points, install AI-driven CCTV surveillance, enforce strict visitor management, and conduct regular security audits to identify and plug operational gaps.
What risks do industries face in India?
Industries in India face significant risks including inventory shrinkage, internal supply chain collusion, fire and safety hazards, and challenges related to regulatory compliance. Managing these requires a proactive, rather than reactive, security posture.
From Cost Center to Operational Asset
Transitioning from reactive guarding to proactive, integrated security marks a vital shift in operational maturity. Treating security as a mere “line-item expense” is a high-stakes gamble; siloing your infrastructure invites inventory shrinkage, compliance breaches, and preventable downtime.
Our “Man + Tech” methodology transforms security from an administrative burden into a predictable, measurable business enabler. Stop waiting for the next “variance” to signal failure. Engineer resilience into your plant’s DNA today.